API Keys
Generating Razorpay API keys, understanding Key ID vs Key Secret, and storing them securely in VaultMate and Supabase secrets.
Razorpay identifies your application using two keys: a Key ID and a Key Secret. Understanding the difference between them is not optional — using them in the wrong place is a security vulnerability with real financial consequences.
Key ID vs Key Secret — The Fundamental Rule
| Key ID | Key Secret | |
|---|---|---|
| Starts with | rzp_test_ or rzp_live_ | A long random alphanumeric string |
| Identifies | Your Razorpay account | Authenticates API requests |
| Safe to put in frontend | Yes | No — never |
| Safe to put in edge functions | Yes | Yes |
| Safe to commit to Git | No | Absolutely not |
| What happens if exposed | Someone knows your account ID | Someone can create orders, issue refunds, access all transaction data |
The CA analogy: the Key ID is like your firm's PAN number — it identifies who you are, and you share it in TDS filings. The Key Secret is like your net banking password — it authorises actions on your account. You would not put your net banking password on a client invoice.
Generating Your API Keys
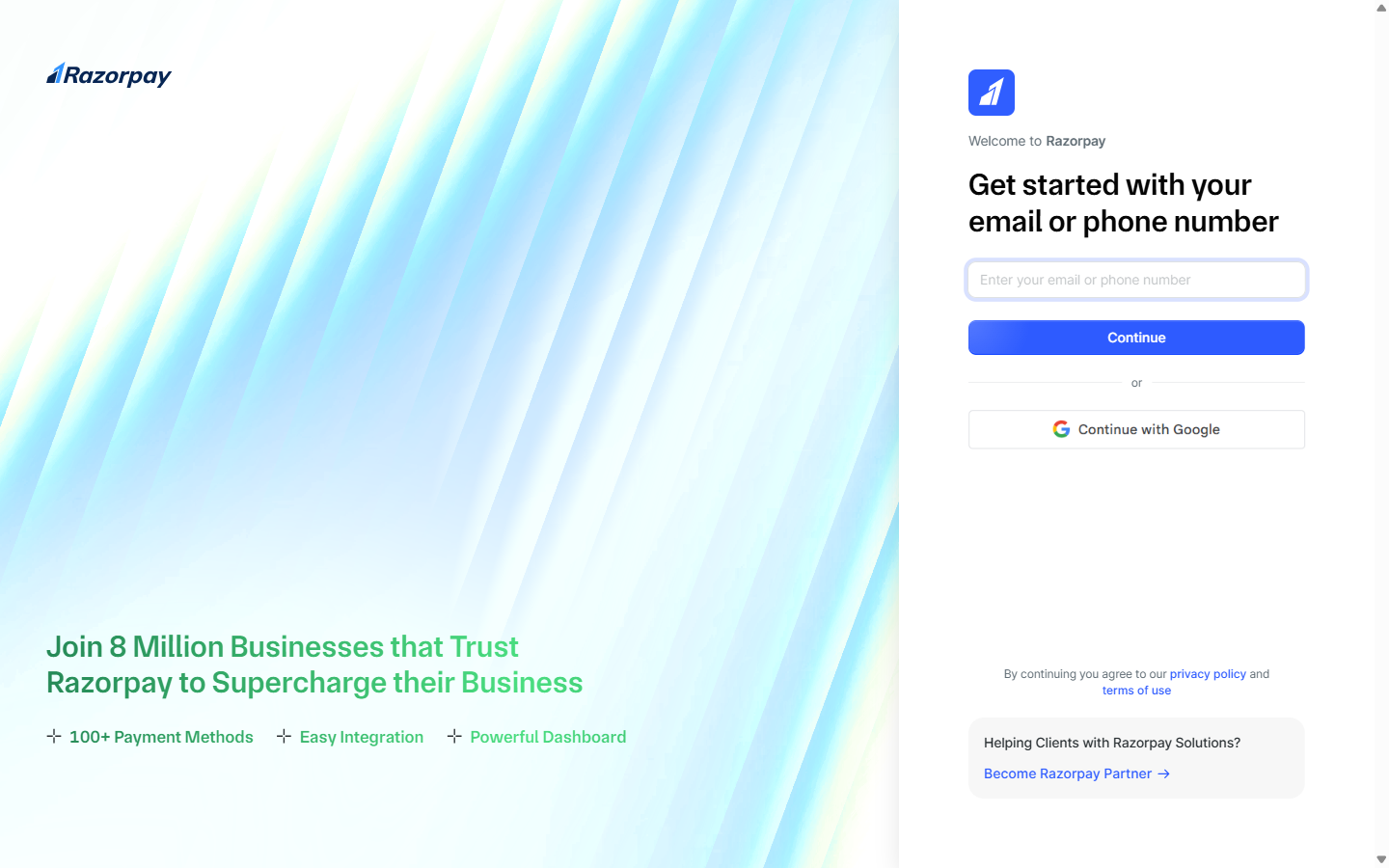
Open API Keys settings
Log into dashboard.razorpay.com. Confirm you are in Test Mode (toggle, top right — should say "Test Mode"). Then in the left sidebar click Settings (gear icon at the bottom) → API Keys.
 Settings → API Keys. Click Generate to create a Test Key pair — Razorpay shows the Key ID and Key Secret one time only.
Settings → API Keys. Click Generate to create a Test Key pair — Razorpay shows the Key ID and Key Secret one time only.
Generate test keys
Click Generate Test Key. A dialog appears showing both keys:
- Key ID:
rzp_test_AbCdEfGhIjKlMn - Key Secret:
AbCdEfGhIjKlMnOpQrStUvWxYz1234567890
The Key Secret is shown only once. Once you close this dialog, you cannot see the Key Secret again — only regenerate it. Regenerating invalidates the old key immediately. Any application using the old key will start failing. Save it right now before closing the dialog.
Save to VaultMate immediately
Open VaultMate from your desktop. Navigate to your project (or create one if it doesn't exist for this project). Click Add Credential and create two entries:
Entry 1 — Key ID:
- Title:
Razorpay Key ID — Test - Category:
API Key - Secret: your Key ID starting with
rzp_test_ - URL:
https://dashboard.razorpay.com - Notes:
Test mode. Switch to rzp_live_ when going to production.
Entry 2 — Key Secret:
- Title:
Razorpay Key Secret — Test - Category:
API Key - Secret: your Key Secret (the long alphanumeric string)
- URL:
https://dashboard.razorpay.com - Notes:
Test mode. Never put this in frontend code or .env.
Save both entries before continuing.
Add Key ID to your frontend environment
In your project's .env.local, add a line for the Key ID (this is safe to put in the frontend because the Key ID is public-facing):
For Vite projects (EduTrack mobile web panel uses Next.js, but note the difference):
Add both keys to Supabase secrets
Your edge functions need both keys. Set them as Supabase secrets (they are stored encrypted, not in your codebase):
To verify they were set:
You should see RAZORPAY_KEY_ID and RAZORPAY_KEY_SECRET in the output (values are masked — this is correct).
supabase secrets set command for that key.Accessing Keys in Edge Functions
Inside a Supabase Edge Function (Deno runtime), access the secrets via Deno.env.get():
This pattern — checking that the secret exists before using it — prevents silent failures where a misconfigured secret causes confusing errors downstream.
Regenerating Keys (When It Becomes Necessary)
You regenerate keys when:
- A key was accidentally committed to Git
- A key was shared in a message, screenshot, or document
- A team member with access to the keys leaves the project
- You suspect unauthorised access (check the Razorpay dashboard for unexpected transactions)
Regeneration procedure:
Regenerate in Razorpay Dashboard
Go to Settings → API Keys → click Regenerate. The moment you click this, the old keys stop working.
Save new keys to VaultMate immediately
Save the new Key ID and Key Secret to VaultMate before doing anything else.
Update your environment file
Update .env.local with the new Key ID.
Update Supabase secrets
Update Supabase secrets with both new values using supabase secrets set.
Update Vercel environment variables
If deployed to Vercel, update the environment variable there too.
Verify with a test payment
Test one payment end-to-end to confirm the new keys are working.
The moment you click Regenerate, the old keys stop working. Any running application using the old keys will start returning authentication errors. Do steps 3–6 without delay.
Key Storage Summary
| Location | Key ID | Key Secret |
|---|---|---|
.env.local | Yes | No |
| VaultMate | Yes | Yes |
| Supabase secrets | Yes | Yes |
| Vercel environment variables | Key ID only (as NEXT_PUBLIC_RAZORPAY_KEY_ID) | Never |
| Git / source code | Never | Never |
| Slack / WhatsApp / email | Never | Never |